You can create multiple policies, for example 7, 8, 9 with different configuration. Routers participating in Phase 1 negotiation tries to match a ISAKMP policy matching against the list of policies one by one. If any policy is matched, the IPSec negotiation moves to Phase 2. Hash sha – SHA algorithm will be used. We created a solution by configuring sVTI and dVTI Sides with 'ip unnumbered' and use RIP to 'discover' the Tunnel IPs on both sides dynamically. This works for the moment, but is not satisfying me. In future i will to migrate the static Routing configuration to aaa-attributes (Locally or on our RADIUS), but for the moment i'm fine with this.
- Dvti Configuration Example
- Dvi Configurations
- Configuring Cisco Easy VPN With IPSec Dynamic Virtual Tunnel ...
IPSec VPN is a security feature that allow you to create secure communication link (also called VPN Tunnel) between two different networks located at different sites. Cisco IOS routers can be used to setup VPN tunnel between two sites. Traffic like data, voice, video, etc. can be securely transmitted through the VPN tunnel. In this post, I will show steps to Configure Site to Site IPSec VPN Tunnel in Cisco IOS Router. You can also setup Configure IPSec VPN With Dynamic IP in Cisco IOS Router.
Configure Site to Site IPSec VPN Tunnel in Cisco IOS Router
Diagram below shows our simple scenario. The two sites have static public IP address as shown in the diagram. R1 is configured with 70.54.241.1/24 and R2 is configured with 199.88.212.2/24 IP address. As of now, both routers have very basic setup like, IP addresses, NAT Overload, default route, hostnames, SSH logins, etc.
There are two phases in IPSec configuration called Phase 1 and Phase 2. Let’s start the configuration with R1. Before you start configuring the IPSec VPN, make sure both routers can reach each other. I have already verified that both routers can ping each other so let’s start the VPN configuration.
Step 1. Configuring IPSec Phase 1 (ISAKMP Policy)
Here is the details of each commands used above,
- crypto isakmp policy 5 – This command creates ISAKMP policy number 5. You can create multiple policies, for example 7, 8, 9 with different configuration. Routers participating in Phase 1 negotiation tries to match a ISAKMP policy matching against the list of policies one by one. If any policy is matched, the IPSec negotiation moves to Phase 2.
- hash sha – SHA algorithm will be used.
- authentication pre-share – Authentication method is pre-shared key.
- group 2 – Diffie-Hellman group to be used is group 2.
- encryption 3des – 3DES encryption algorithm will be used for Phase 1.
- lifetime 86400 – Phase 1 lifetime is 86400 seconds.
- crypto isakmp key cisco@123 address 199.88.212.2 – The Phase 1 password is cisco@123 and remote peer IP address is 199.88.212.2.
Step 2. Configuring IPSec Phase 2 (Transform Set)
Here is the detail of command used above,
- crypto ipsec transform-set MY-SET – Creates transform-set called MY-SET
- esp-aes – AES encryption method and ESP IPSec protocol will be used.
- esp-md5-hmac – MD5 hashing algorithm will be used.
- crypto ipsec security-association lifetime seconds – This is the amount to time that the phase 2 session exists before re-negotiation.
Step 3. Configuring Extended ACL for interesting traffic.
This ACL defines the interesting traffic that needs to go through the VPN tunnel. Here, traffic originating from 192.168.1.0 network to 192.168.2.0 network will go via VPN tunnel. This ACL will be used in Step 4 in Crypto Map.
Step 4. Configure Crypto Map.
Here is the detail of command used above,
- crypto map IPSEC-STE-TO-STE-VPN 10 ipsec-isakmp – Creates new crypto map with sequence number 10. You can create more sequence numbers with same crypto map name if you have multiple sites.
- match address VPN-TRAFFIC – Its matches interesting traffic from ACL named VPN-TRAFFIC.
- set peer 199.88.212.2 – This is public IP address of R2.
- set transform-set MY-SET – This links the transform-set in this crypto map configuration.
Step 5. Apply Crypto Map to outgoing interface of R1.
Step 6. Exclude VPN traffic from NAT Overload.
Above ACL 101 will exclude interesting traffic from NAT.
Now, repeat same steps in R2.
Step 1. Configuring IPSec Phase 1 (ISAKMP Policy)
Step 2. Configuring IPSec Phase 2 (Transform Set)
Step 3. Configuring Extended ACL for interesting traffic.
Step 4. Configure Crypto Map.
Step 5. Apply Crypto Map to outgoing interface
Step 6. Exclude VPN traffic from NAT Overload.
Verification and testing.
To test the VPN connection let’s ping from R1 to PC2.
As you can see, the ping from R1 to PC2 is successful. Don’t forget to ping from inside IP address while testing the VPN tunnel from the router. You can also ping from PC1 to PC2.
To verify the IPSec Phase 1 connection, type show crypto isakmp sa as shown below.
To verify IPSec Phase 2 connection, type show crypto ipsec sa as shown below.
You can also view active IPSec sessions using show crypto session command as shown below.
In this way you can configure Site to Site IPSec VPN tunnel in Cisco IOS Router.
You may also like -
- Why Backup your Microsoft Office 365 - November 27, 2020
- RDP Connection Freezes in Windows 10 - August 17, 2020
- Upgrade Windows 10 Home to Pro - August 11, 2020
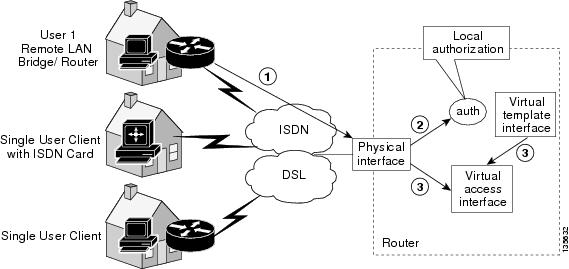
In this section we will configure a hub router that is able to offer VPN tunnelsto a unknown number of dynamic VPN peers
This is useful where you may need to rapidly deploy a varied number of sitesand do not want to have to reconfigure the hub router everytime a new siteis activated.
The configuration we will be putting in place is suitable whenthe remote peers are using dynamic IP addressing but note that as we areusing pre-shared key authentication the same key will be accepted from anyIP address. This is not as secure as it could be and in a productiondeployment the use of digital signatures should be considerd.
It is assumed that the router already have basic IP connectivity and WANrouting is in place.
After the IPSec tunnel is configured working we will also setup dynamic routingthrough the tunnel.
Configuration Steps¶
On all devices:#. Configure a loopback to use a tunnel IP#. Configure the Keyring#. Configure the ISAKMP Policy#. Configure the ISAKMP Profile#. Configure the IPSec Proposal#. Configure the IPSec Profile#. Configure dynamic routing
On the Hub:#. Configure the tunnel interface template
On the Spokes:#. Configure a static tunnel interface
Step 1: Define the Loopback Interface¶
Step 1: Define the PSK Keyring¶
For the hub it’s necessary to define a wildcard PSK if the spokes willbe using dynamic IP addresses. If they will be static they can be definedindividually but that would loose some of the flexibility of the solution.
On the spokes the PSK can be defined with just the Hubs IP:.. code-block:: none
- crypto keyring <keyring-name>
- pre-shared-key address <hub-ip> key <psk>
Step 1: Configure the ISAKMP Policy¶
Step 3: Configure the ISAKMP Profile¶
Step 4: Configure the IPSec Transform Set¶
Step 5: Configure the IPSec Profile¶
Dvti Configuration Example
Step 6: Define the tunnel interfaces¶
On the Hub we will configure a template that will be cloned each time aclient connects.
On the Spokes we can configure a nubmer tunnel interface:
Complete Example¶
The Hub config could be performed as follows:
The Spokes could then be configured as follows:
Dvi Configurations
When ever a new spoke needs to be deployed the same config as above can be used,just change the following:
Configuring Cisco Easy VPN With IPSec Dynamic Virtual Tunnel ...
- Loopback IP
- Subnets advertised by routing protocol
